Data Engineering Integration
- Data Engineering Integration 10.4.1
- All Products

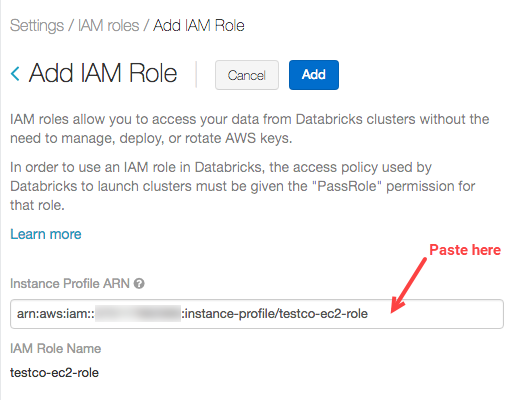
{ "Effect": "Allow", "Action": "iam:PassRole", "Resource": "arn:aws:iam::<aws-account-id-databricks>:role/<iam-role-for-s3-access>" },