PowerCenter
- PowerCenter 10.5
- All Products

Option
| Description
|
|---|---|
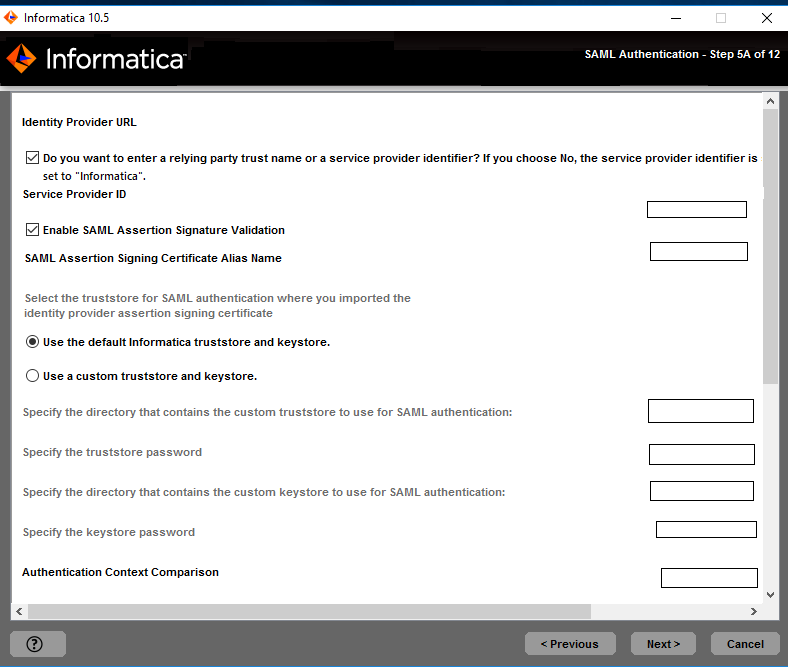
Use the default Informatica SSL certificate file.
| Select to use the default Informatica truststore file for SAML authentication.
|
Enter the location of the SSL certificate file.
| Select to use a custom truststore file for SAML authentication. Specify the directory containing the custom truststore file on gateway nodes within the domain. Specify the directory only, not the full path to the file.
|
Option
| Description
|
|---|---|
Use the default Informatica SSL certificate file.
| Select to use the default Informatica truststore file for SAML authentication.
|
Enter the location of the SSL certificate file.
| Select to use a custom truststore file for SAML authentication. Specify the directory containing the custom truststore file on gateway nodes within the domain. Specify the directory only, not the full path to the file.
|
Property
| Description
|
|---|---|
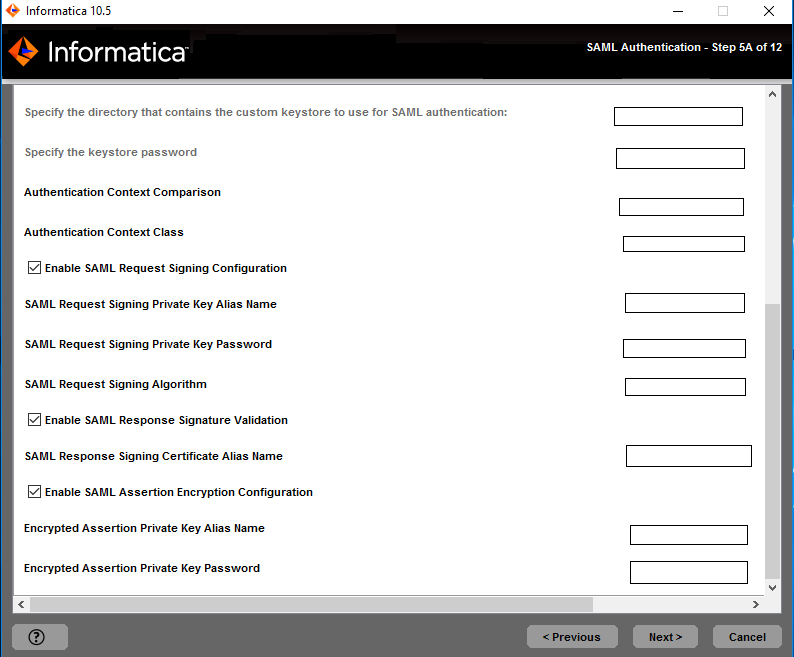
Truststore Directory
| Specify the directory containing the custom truststore file on gateway nodes within the domain. Specify the directory only, not the full path to the file.
|
Truststore Password
| The password for the custom truststore file.
|
Keystore Directory
| Specify the directory containing the custom keystore file.
|
Keystore Password
| The password for the custom keystore file.
|