PowerCenter
- PowerCenter 10.5.4
- All Products

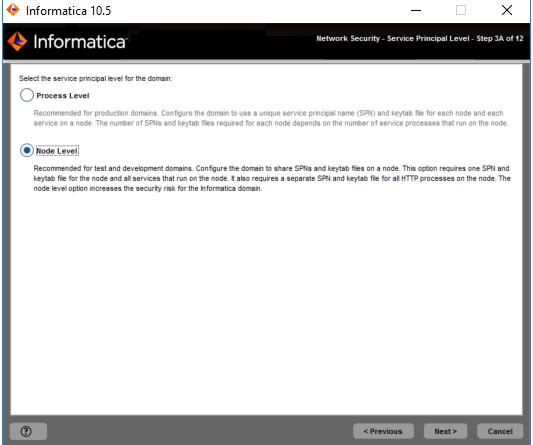
Level
| Description
|
|---|---|
Process Level
| Configures the domain to use a unique service principal name (SPN) and keytab file for each node and each application service on a node.
The number of SPNs and keytab files required for each node depends on the number of application service processes that run on the node. Use the process level option for domains that require a high level of security, such as productions domains.
|
Node Level
| Configures the domain to share SPNs and keytab files on a node.
This option requires one SPN and keytab file for the node and all application services that run on the node. It also requires a separate SPN and keytab file for all HTTP processes on the node.
Use the node level option for domains that do not require a high level of security, such as test and development domains.
|