Administrator
- Administrator
- All Products

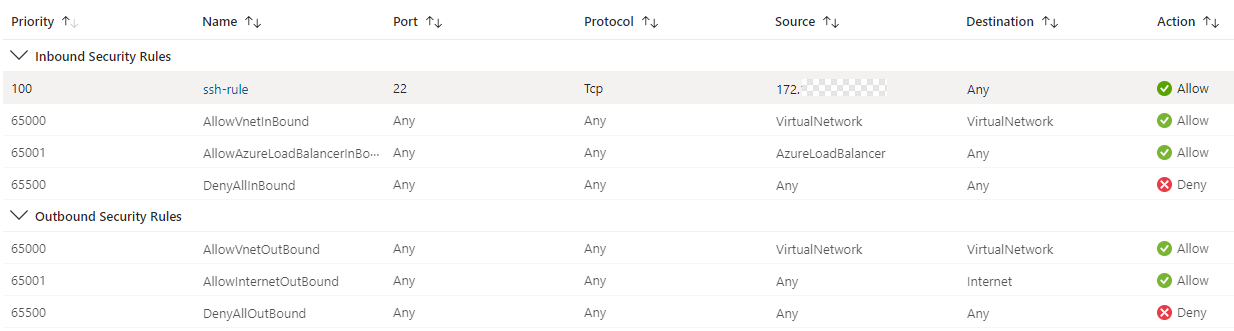
Rule
| Description
|
|---|---|
SSH access
| You need this rule only for troubleshooting. It isn't used by
Data Integration .
For example, you can use this rule to pull logs from worker nodes. Configure this rule the same way as the
master node's NSG.
|
Azure inbound
| The default inbound rules are the same as the
master node's NSG.
|
TCP inbound
| Allow incoming traffic from TCP ports 10250, 10257, and 10259.
|
